Crypto-Stealing Malware Surges as Scammers Impersonate AI, Web3 Startups — Here’s the Catch
A new wave of sophisticated crypto-stealing malware is spreading across the internet as scammers create fake AI, gaming, and Web3 startups to lure victims into downloading malicious software.
Cybersecurity firm Darktrace has raised the alarm, detailing how these campaigns operate through elaborate social engineering tactics that exploit trust in digital startups.
Attackers are setting up fake companies with convincing websites, social media profiles, GitHub repositories, white papers, and even fake team pages on platforms like Notion.
Many of the sites also appear to be linked to verified or compromised X (formerly Twitter) accounts to appear more legitimate. The fake accounts often post software updates, blog content, and product announcements to maintain the illusion of authenticity.
“Threat actors are going to great lengths to make these fake startups look real,” the firm stated, adding that the scam has already impacted users globally.
Victims are often contacted directly on platforms like X, Telegram, or Discord, with the impersonators presenting themselves as employees of the fake firms, offering cryptocurrency in exchange for testing their software.
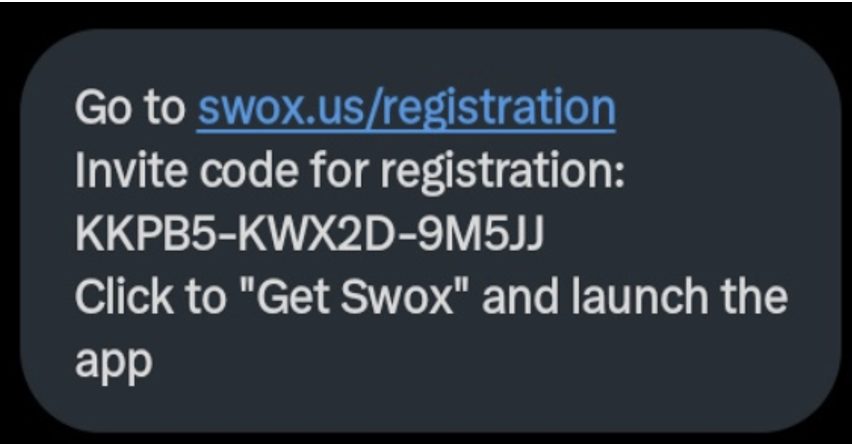
Users are then given a registration code and directed to download malware-infected applications from professional-looking websites.
 Source: Darktrace
Source: Darktrace
Darktrace Warns of Advanced Malware Campaign Targeting Crypto Users
One of the identified schemes involved a fake blockchain game called “Eternal Decay,” which used altered images to claim conference participation and listed fake investors. Gameplay images were also lifted from another game called “Zombie Within.” Other noted fake startups include names like Pollens AI, Swox, and Buzzu, with nearly identical branding and codebases.
According to Darktrace, the malware, targeting both Windows and macOS users, is capable of stealing crypto wallet credentials and personal information, using tools like the Realst and Atomic Stealer malware families.
Darktrace technical analysis shows that on Windows, the attackers use Electron-based apps to perform system profiling, download malicious files, and execute them quietly.
On macOS, a disguised DMG file installs the Atomic Stealer, which collects browser data, wallet credentials, and other sensitive files before sending them to attacker-controlled servers.
Darktrace noted that the malware includes advanced evasion techniques, such as stolen software signing certificates, obfuscation, and persistent background execution to avoid detection.
“This is one of the more elaborate and persistent social engineering campaigns we’ve seen targeting the crypto space,” said a Darktrace researcher familiar with the investigation.
“They’re building out fake companies with all the digital trimmings — even fake merchandise stores and doctored company registrations — just to get users to download malware,” they added.
Notably, Darktrace believes the tactics resemble those previously linked to a malware group known as “CrazyEvil,” identified by Recorded Future earlier this year. That group was known for targeting crypto users and developers through fake projects and social engineering techniques.
While it’s unclear whether CrazyEvil is directly responsible for this campaign, the tactics appear consistent. Darktrace warned that the threat actors are using newer variants of malware and more elaborate deception methods to lure victims.
Malware Campaigns and Credential Breaches Fuel 2025 Crypto Crime Surge
The rise in crypto-targeted scams hasn’t slowed down, and now, a wave of highly coordinated malware and credential breaches is pushing 2025 toward record-breaking crypto losses.
According to Kaspersky’s Financial Cyberthreats report, crypto phishing detections have surged 83.4% year-over-year, while mobile banking Trojan attacks have increased 3.6x.
In contrast, traditional banking malware has declined, indicating a shift in attacker priorities from fiat systems to crypto wallets.
One of the most alarming developments is “SparkKitty,” a sophisticated mobile malware strain active since February 2024.
Notably, the tool, which was disguised as TikTok mods or crypto apps, has infiltrated Google Play and the App Store, bypassing security checks to steal seed phrases stored in user photo galleries.
SparkKitty, an evolution of the earlier SparkCat campaign, uses OCR technology to scan screenshots of wallet credentials from infected devices.
Meanwhile, in May, cybersecurity analysts traced malware back to Procolored, a Chinese printer manufacturer. The printer’s official drivers carried a crypto-stealing remote access trojan, replacing copied wallet addresses with those of attackers.
The scheme went undetected for six months, resulting in the theft of 9.3 BTC, worth nearly $1 million.
Adding to the threat, a massive data breach uncovered by Cybernews revealed over 16 billion login credentials, many collected via infostealer malware.
The breach included sensitive access data from platforms like Telegram, GitHub, and Apple, escalating risks for crypto users managing assets online.
Combined with CertiK’s estimate of $2.2 billion lost to crypto attacks in H1 2025, these incidents indicate the growing sophistication of cybercrime targeting digital assets.
You May Also Like

Lovable AI’s Astonishing Rise: Anton Osika Reveals Startup Secrets at Bitcoin World Disrupt 2025

How to Check Your SASSA SRD Grant Status in 2025 (Complete Guide for Applicants)






