Palo Alto Networks NGTS to Automate Digital Trust
Palo Alto Networks Launches NGTS: Rewiring Digital Trust for a Post-Quantum, Always-On Economy
Palo Alto Networks has just launched Next-Generation Trust Security (NGTS), and this isn’t just another cybersecurity release. It signals a deeper shift in how trust is managed, enforced, and experienced.
When Trust Fails, Experience Fails
When digital trust breaks, the failure is not incremental—it is absolute. Applications go offline, transactions halt, and customer confidence erodes instantly. This is the new reality enterprises face as certificate lifecycles shrink and cryptographic standards evolve faster than operational models can keep up.
Palo Alto Networks has introduced Next-Generation Trust Security (NGTS) at a moment when trust itself is becoming dynamic, volatile, and mission-critical. The announcement is not just about improving certificate lifecycle management—it signals a structural shift in how trust is governed across digital systems.
So what?
Trust is no longer a backend security function—it is now a frontline determinant of customer experience and business continuity.
The Collapse of Static Trust Models
For decades, digital certificates functioned as long-lived identity markers—issued, deployed, and largely forgotten. That paradigm is now collapsing under three simultaneous pressures:
- Certificate lifecycles shrinking by over 90%
- Increasing frequency of trust authority disruptions
- The emergence of post-quantum cryptographic requirements
At a structural level, enterprises are entering a state of continuous cryptographic reset. Systems must constantly validate, renew, and adapt trust relationships across applications, clouds, and networks.
Legacy models—spreadsheet-driven tracking, siloed ownership, and manual renewals—are fundamentally misaligned with this new reality. They introduce latency into processes that now demand real-time responsiveness.
This becomes critical when even a single expired certificate can cascade into system-wide outages, directly impacting customers.
So what?
The industry is shifting from static trust validation to continuous trust orchestration, redefining reliability as a real-time capability rather than a periodic checkpoint.
Moving Trust into the Network Control Plane
Strategically, Palo Alto Networks is redefining where and how trust is managed. NGTS embeds certificate lifecycle management directly into the network layer, transforming trust into a centrally orchestrated, continuously enforced capability.
The shift here is profound:
- From manual processes → automated systems
- From team-based ownership → network-level control
- From reactive management → proactive orchestration
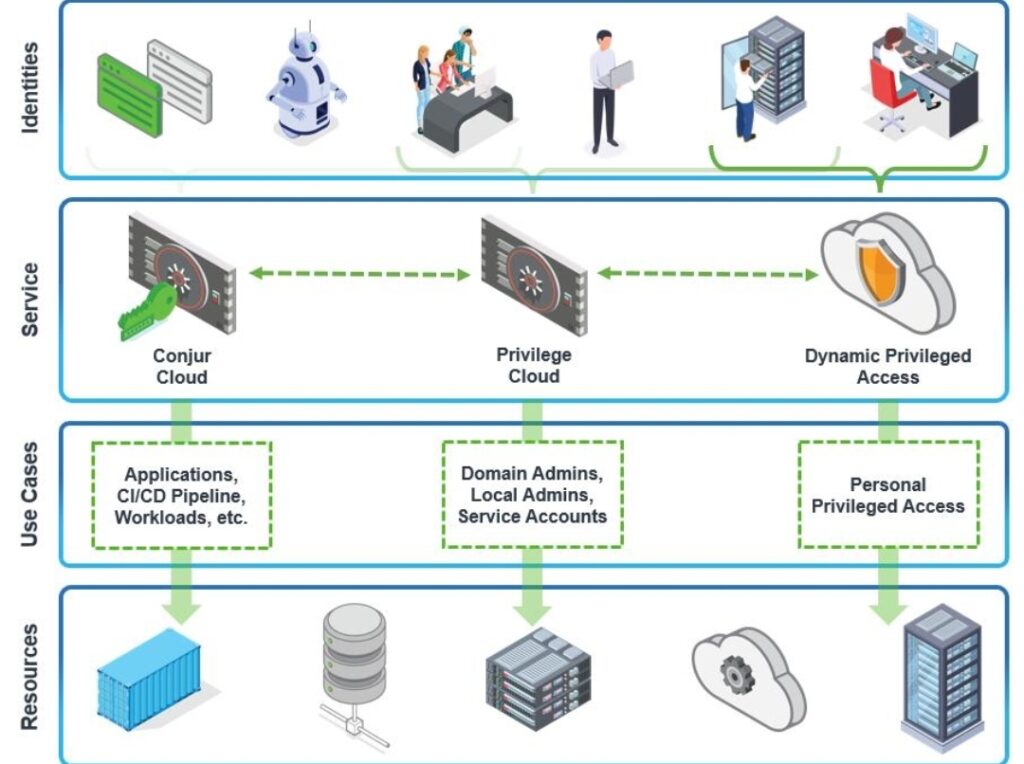
By integrating machine identity intelligence from CyberArk, Palo Alto Networks is also bridging the long-standing gap between identity security and operational uptime.
This is where the shift occurs—from managing certificates as isolated assets to governing trust as a system-wide control layer.
So what?
Palo Alto Networks is positioning itself not just as a security provider, but as a control-plane owner for operational resilience, a significantly higher strategic layer.
From Tools to Control-Plane Ownership
The competitive landscape reveals a clear stratification:
- CLM Vendors: Focused on discovery and renewal automation, but operate outside the network
- Security Platforms: Offer broader protection but lack deep integration between trust and enforcement
- Legacy Tools: Reactive, siloed, and operationally limited
NGTS differentiates by collapsing these layers into a unified system where visibility, automation, and enforcement coexist within the network fabric.
The deeper implication is that competition is no longer about feature richness—it is about who owns the enforcement layer of trust.
So what?
Control-plane ownership creates defensibility. It is harder to displace a platform embedded into the network than a tool layered on top of it.
Turning Trust into a Continuous System Capability
NGTS operates as a network-native orchestration engine for cryptographic trust.
Core Components:
- Certificate Lifecycle Management (CLM)
- Real-time network visibility
- Automated enforcement mechanisms
- Machine identity intelligence via CyberArk
Operational Flow:
- Discover certificates across applications and services
- Map trust dependencies across environments
- Automate renewals and replacements
- Enforce compliance in real time at the network layer
Unlike legacy approaches that isolate certificate management, NGTS creates a closed-loop system—one that continuously monitors, updates, and enforces trust without manual intervention.
Operationally, this translates into:
- Elimination of shadow certificates
- Reduction in renewal delays
- Prevention of outage-triggering failures
So what?
Trust becomes a self-regulating system property, not an operational burden—enabling enterprises to scale securely without increasing complexity.
From Security Function to Experience Guarantee
From a CX standpoint, NGTS addresses a critical but often invisible failure point: certificate-driven service disruption.
Customer Impact:
- Seamless digital interactions
- Reduced downtime across services
- Increased confidence in platform reliability
Business Impact:
- Lower incident response costs
- Reduced revenue leakage from outages
- Improved SLA performance
System Impact:
- Continuous trust validation
- Automated remediation
- Reduced operational friction
Before NGTS:
- Failures were reactive
- Ownership was fragmented
- Recovery was costly
After NGTS:
- Failures are prevented
- Ownership is centralized
- Systems self-correct
This becomes critical when customers perceive outages not as technical issues, but as experience failures.
So what?
Cybersecurity is no longer just about protection—it is about ensuring uninterrupted experience delivery, making it a core CX function.
Toward Autonomous Trust Infrastructure
NGTS represents a move toward predictive and autonomous infrastructure maturity.
At this level:
- Systems anticipate failure conditions
- Automation replaces manual intervention
- Trust adapts dynamically to environmental changes
However, a gap remains:
- Integration with legacy systems
- Organizational alignment across teams
The trigger for adoption is clear—shrinking certificate lifecycles and post-quantum readiness demands.
So what?
Enterprises that fail to evolve risk falling into a maturity gap where operational complexity outpaces their ability to maintain trust.
The Cost of Inaction is Rising
From a decision-making perspective, NGTS reframes the conversation:
Build vs Buy vs Partner:
- Build: Impractical due to complexity
- Buy: Most viable path
- Partner: Critical for ecosystem integration
Risk Assessment:
- Adoption risk: Medium (integration challenges)
- Non-adoption risk: High (outages, compliance failures)
Implementation Complexity: High
Requires cross-functional alignment and infrastructure integration
This becomes critical when the cost of failure—both financial and reputational—continues to rise.
So what?
The real decision is not whether to adopt automated trust systems, but how quickly enterprises can operationalize them.
Reshaping Talent, Platforms, and Ecosystems
The introduction of NGTS signals broader industry shifts:
Talent:
Demand will increase for hybrid expertise in network security, cryptography, and automation
Competition:
Vendors will compete on platform integration and control-plane ownership
Ecosystem:
Partnerships like Palo Alto Networks and CyberArk will define future architectures
This is where the shift occurs—from fragmented tooling ecosystems to integrated trust platforms.
So what?
The industry is moving toward consolidation around platforms that can orchestrate trust end-to-end.
The Rise of Continuous Trust Architecture
As quantum computing advances and encryption standards evolve, enterprises will face constant cryptographic change. Static models will become obsolete.
NGTS represents an early blueprint for continuous trust architecture, where:
- Trust is dynamic
- Enforcement is automated
- Systems are self-healing
The deeper implication is that trust will become as fundamental—and as automated—as networking itself.
So what?
Organizations that adopt early will gain not just security advantages, but experience reliability as a competitive differentiator.
What Leaders Must Internalize
- Trust is shifting from periodic validation to continuous orchestration
- The network is emerging as the control plane for trust enforcement
- Certificate failures are now CX-critical events
- Automation is becoming essential for post-quantum readiness
- Platform ownership will define competitive advantage in cybersecurity
Final Insight:
Palo Alto Networks’ NGTS is not just solving for certificate management—it is redefining trust as a living, automated layer of the digital experience stack.
The post Palo Alto Networks NGTS to Automate Digital Trust appeared first on CX Quest.
You May Also Like

Oil: Prices slump below $100 on ceasefire – ING

Thailand SEC Targets Hidden Crypto Funding With New Rules






